Common Access Control Mistakes and How to Avoid Them
Common Access Control Mistakes and How to Avoid Them Introduction Access control is a critical element in ensuring
Common Access Control Mistakes and How to Avoid Them Introduction Access control is a critical element in ensuring
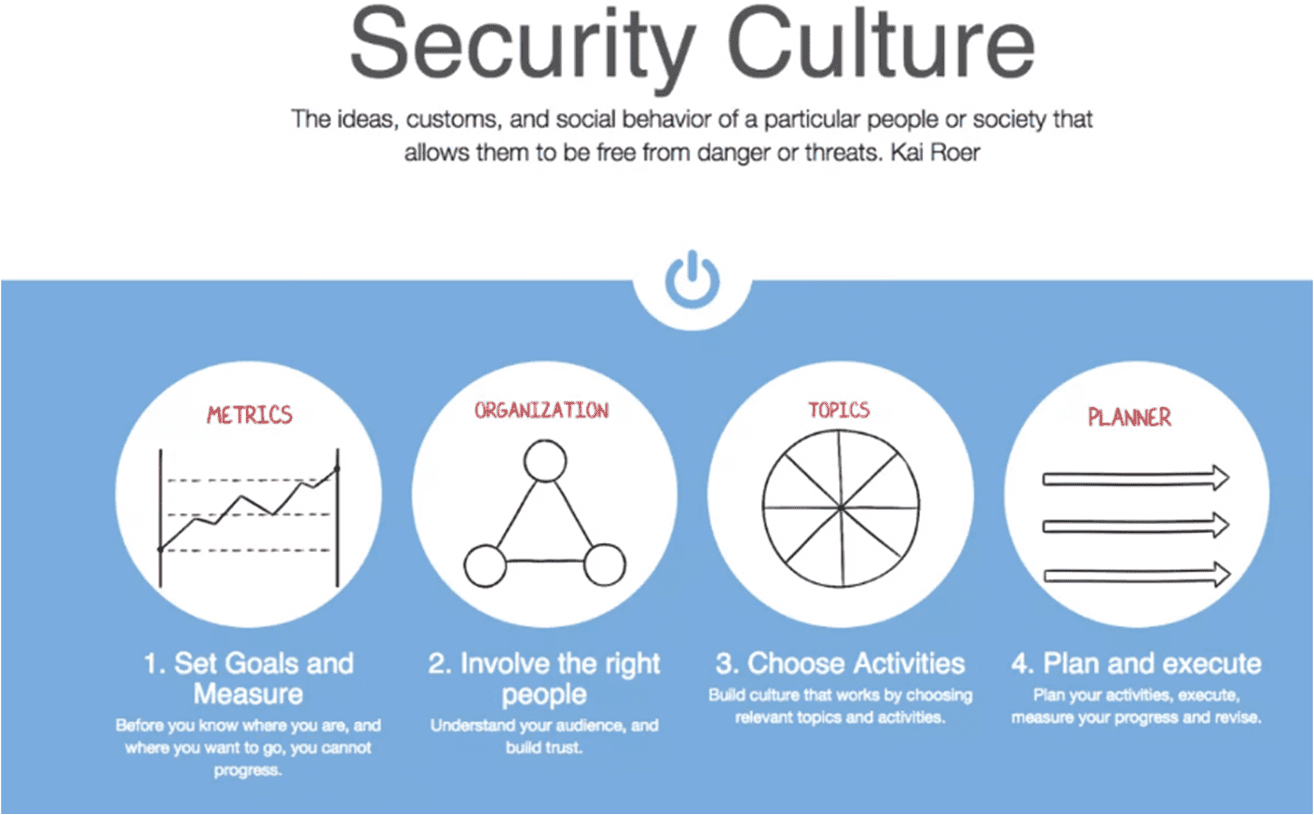
How to Build a Robust Security Culture within Your Organization Welcome to the digital age where organizations face
VoIP Security: Safeguarding Your Business Conversations In today’s digital era, Voice over Internet Protocol (VoIP) has become an
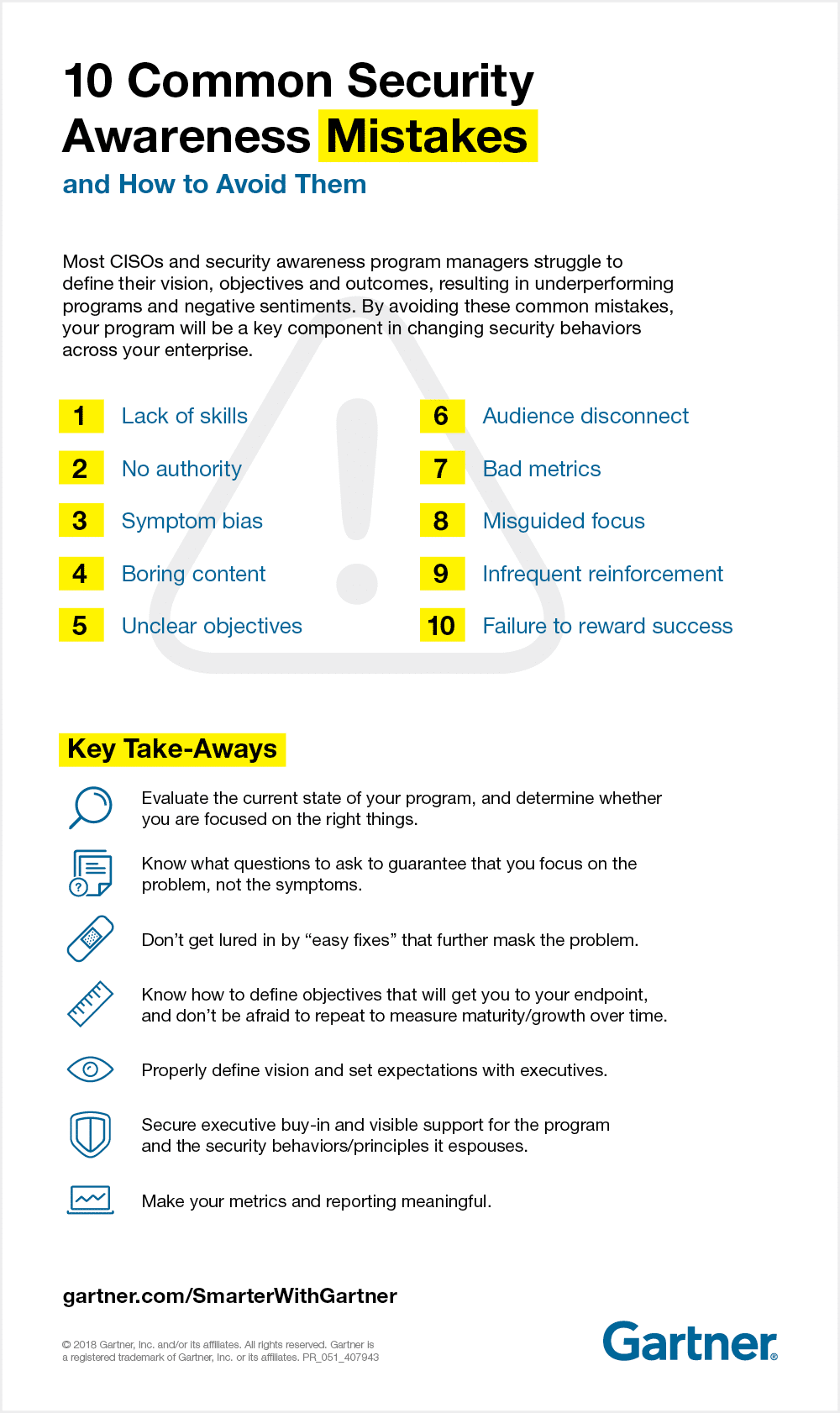
When it comes to digital security, access control is key. Common mistakes such as weak authentication, default settings, and lack of periodic auditing can lead to serious data breaches. Taking the time to properly implement access control strategies can protect sensitive data and ensure system security.
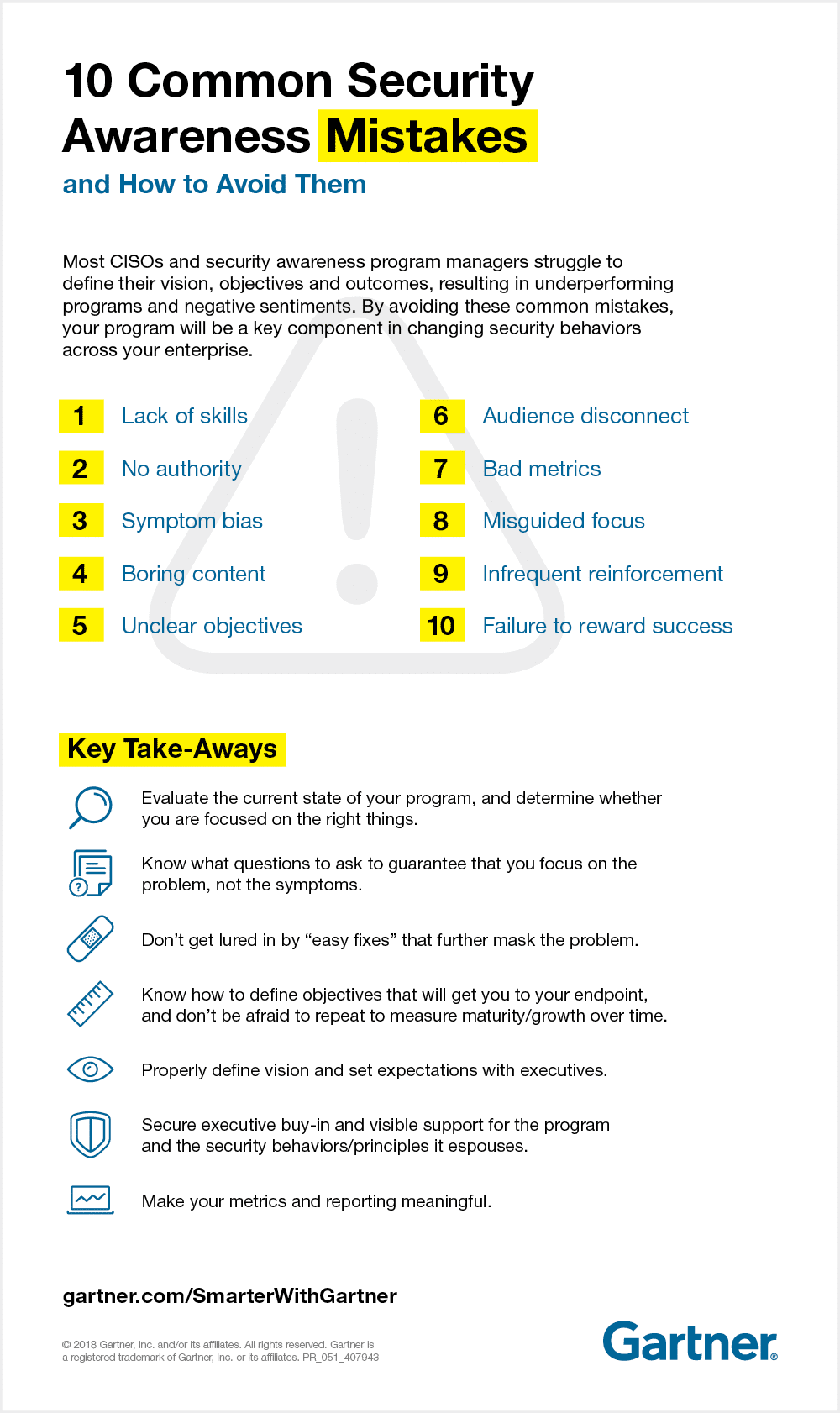
In any organization, access control must be taken seriously. Common mistakes include poor password policies and failing to restrict access to sensitive data. Taking the right precautions can prevent data breaches and unauthorized access.
Easily managed access control systems are essential for any business; they ensure only authorized personnel can enter secure areas, helping to keep your business secure from external threats.
Having reliable IT support is essential for businesses in today’s technology-driven world. Here are the top 10 reasons why professional IT support is essential for your business.
Maintaining secure conversations is essential for businesses of all sizes. In this article, we look at the different security protocols available to ensure your VoIP network is safe and your conversations remain confidential.
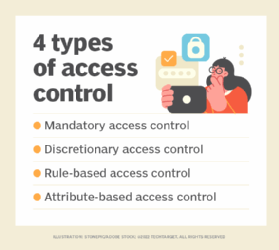
Access control is the silent guardian of security, standing tall to protect valuable assets. Like a secret agent, it grants or denies entry with precision and accuracy. Understanding its importance is crucial in the ever-evolving world of security. Let’s delve into this covert operation and unravel its secrets, ensuring a secure future for all.

In the bustling world of shared office spaces, ensuring access control is crucial for maintaining a harmonious and secure environment. From digital key cards to biometric scanners, innovative solutions are being employed to safeguard against unauthorised entry. As the lines between personal and communal workspaces blur, finding the perfect balance between convenience and security remains a top priority. With technology as our ally, we can create a future where flexibility and privacy coexist seamlessly.

In an ever-evolving world, ensuring physical security is paramount. Access control systems have emerged as the knight in shining armor. From biometric identification to keyless entry, these marvels of technology provide a seamless solution to safeguard sensitive areas. With their ability to restrict unauthorized access and provide a comprehensive audit trail, enhancing physical security has never been more efficient. Embrace the power of access control and bid farewell to security concerns, one locked door at a time.
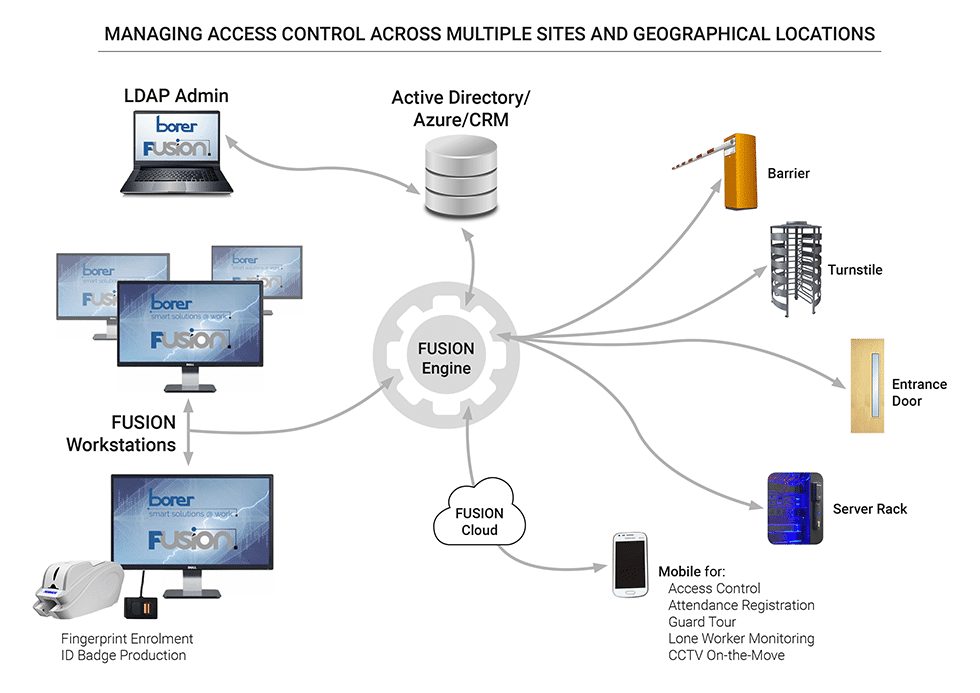
As multi-location businesses continue to expand, the importance of robust access control systems becomes paramount. From corporate buildings to retail stores, ensuring authorized personnel have seamless entry while keeping out uninvited guests is crucial. With advanced technologies like biometric authentication and centralized management, these systems offer a perfect blend of convenience and security. By implementing tailored access control solutions, businesses can safeguard their assets, protect sensitive data, and maintain smooth operations across all locations. Stay one step ahead in the multi-location game with state-of-the-art access control systems.
In a digital age where cyber threats loom large, safeguarding your business is paramount. That’s where robust access control systems come into play – the ultimate armor for your organization. From biometric authentication to smart card readers, these cutting-edge solutions fortify your perimeter, deterring unauthorized access and ensuring only the right people enter. Stay one step ahead in the realm of security and keep your business safe with an impenetrable fortress that leaves no room for compromise.

Title: Crafting a Safer Tomorrow: Evolution of Access Control in Manufacturing Facilities
As the sun slowly rises over the manufacturing landscape, a quiet transformation takes place. Gone are the clunky lock-and-key mechanisms, replaced by a symphony of cutting-edge access control systems. Innovations in safety and security have become the cornerstone of manufacturing facilities, ensuring a seamless blend of efficiency and confidentiality. In this article, we explore the vital role of access control in modern factory ecosystems, unveiling a vivid tapestry of safeguards that promise a brighter future.
In this ever-evolving digital era, securing our cyber existence poses unprecedented challenges. The digital age’s common security issues continue to mount, transforming the online world into a potential battleground. From data breaches to identity theft, this article dives into the intricate web of security challenges we confront daily, highlighting the urgent need for robust online defense mechanisms.
Exploring the realm of VoIP security unveils the fortress of encryption and authentication. As the lifeblood of modern communication, Voice over Internet Protocol requires impenetrable protection. Prepare to delve into the fascinating world where advanced encryption algorithms guard your conversations, while robust authentication mechanisms verify identities. Together, they form an impregnable shield, ensuring your VoIP experience remains secure, reliable, and truly transformative.

Title: The Battle of Access Control: Biometric vs. Card-based Systems
Excerpt:
In the realm of access control, a fierce rivalry prevails as biometric and card-based systems go head-to-head. Like ancient gladiators, these technologies vie for supremacy, captivating the hearts of security enthusiasts worldwide. Each offers unique advantages, but which will triumph in this epoch-making bout? Let’s delve into the intricate world of access control and witness the clash of the titans.

As business owners, ensuring the safety and security of our premises is crucial. But with so many access control systems available, the task of choosing the right one can seem daunting. Fear not! This article will guide you through the process, helping you select an access control system that seamlessly blends innovation, affordability, and adaptability tailored to your business needs. So let’s explore the world of access control systems and pave the way for a secure future!
Typically replies within a day
We are available 24/7 with priority support via our website form, email and WhatsApp channel. Please note our WhatsApp number is the same as our office number below.
We have mobile branches in Roodepoort, Krugersdorp and Randburg by appointment only.
Welcome to Chellu Solutions! These Terms and Conditions govern your use of our website, www.chellu.tech, as well as any services provided by Chellu Solutions. By accessing or using our website or engaging in any services offered by Chellu Solutions, you agree to be bound by these Terms and Conditions. These terms apply to all interactions with Chellu Solutions, including but not limited to website usage, service agreements, and any business transactions. If you do not agree with any part of these terms, please refrain from using our website and services.
In order to access certain services on our website, such as making purchases, enrolling in courses, or accessing our client zone, you must create a user account. You agree to provide accurate and up-to-date information during the registration process and to keep your account details secure.
You are responsible for maintaining the confidentiality of your account credentials and for any activity that occurs under your account. We reserve the right to suspend or terminate your account if we suspect any unauthorized use or violation of these Terms and Conditions.
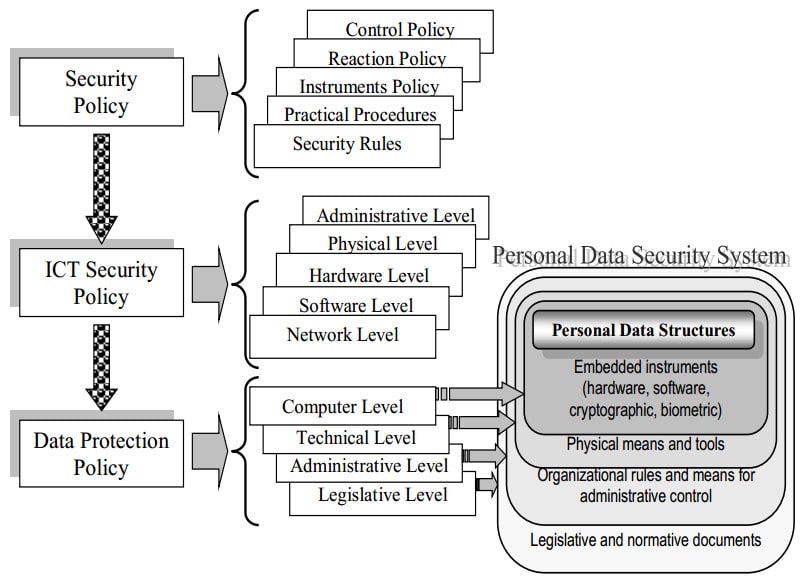
We collect personal information, including names, email addresses, phone numbers, IP addresses, and other relevant details, for the purpose of providing and improving our services. We may use this information to communicate with you, process your orders, provide support, and personalize your experience on our website.
We use cookies and similar tracking technologies to enhance your browsing experience, analyze website traffic, and for marketing purposes. By using our website, you consent to the use of cookies in accordance with our Privacy Policy.
Our website may integrate with third-party services, such as Google, Microsoft, Plesk, Uniform Domains, Facebook, Chellu CRM, and 3cx. These services may have their own terms and privacy policies, and your use of their services is subject to their respective terms.
We take reasonable technical and organizational measures to protect the personal information we collect and prevent unauthorized access, loss, or destruction of data. However, please note that no method of data transmission over the internet or electronic storage is completely secure, and we cannot guarantee absolute data security.
We do not share your personal data with unauthorized third-party companies. However, we may disclose your information if required by law or if necessary to protect our rights, property, or safety, or the rights, property, or safety of others.
You have the right to access, modify, or delete the personal information we hold about you. You can update your account details or contact us to exercise these rights.
We comply with the Protection of Personal Information Act (POPIA) as per South African law. We are committed to handling your personal information in accordance with applicable data protection laws and regulations.
All payments for services provided by Chellu Solutions must be made in accordance with the agreed-upon invoicing schedule. Failure to make timely payments may result in service suspension as outlined below.
In the event of a failed payment on any invoice, Chellu Solutions reserves the right to suspend all services associated with your account, including fully paid services. Service suspension may occur if outstanding balances remain unpaid beyond the due date specified on the invoice. Services will only be reinstated once full payment has been received and processed.
It is the client’s responsibility to communicate any delays in payment and to make a reasonable arrangement to settle the account in full. Failure to do so may result in service suspension until the outstanding balance is paid.
Clients may request service cancellation by providing written notice. For month-to-month agreements, a one-month calendar notice is required. If on a fixed-term contract, written cancellation notice must be given within one month of the contract’s expiration. Long-term agreements will automatically renew unless cancellation notice is provided in time, in which case the agreement will be extended for the same duration as the previous term.
Chellu Solutions reserves the right to terminate or suspend services due to non-payment, violation of these Terms and Conditions, or any activity deemed harmful to our systems, other users, or third parties.
Chellu Solutions will inform clients of any price increases within a reasonable timeframe as communicated by our suppliers. However, some suppliers may implement price increases without prior notice, and we cannot guarantee advance notification in such cases.
Chellu Solutions shall not be liable for any indirect, incidental, or consequential damages arising from the use of our services, including but not limited to data loss, service interruptions, or third-party failures. Our liability shall be limited to the amount paid for the affected service.
Clients must use our services responsibly and in compliance with applicable laws. Prohibited activities include, but are not limited to, spamming, hacking, and hosting illegal content. Violation of this policy may result in immediate termination of services.
Chellu Solutions reserves the right to modify, discontinue, or upgrade services at any time. Reasonable efforts will be made to notify clients of significant changes.
These Terms and Conditions are governed by South African law. Any disputes shall be resolved in the appropriate courts of South Africa.
Clients agree to keep any confidential information received from Chellu Solutions private and not disclose it to unauthorized parties.
Chellu Solutions is not liable for any failure to perform due to circumstances beyond our control, including natural disasters, cyber-attacks, government actions, or other unforeseeable events.
We reserve the right to modify or update these Terms and Conditions and the Privacy Policy at any time. Any changes will be effective upon posting the revised versions on our website. We encourage you to review these policies periodically to stay informed about any updates.
If you have any questions or concerns about these Terms and Conditions, please contact us at admin@chellu.tech.
Please refer to the separate document titled “Privacy Policy” for detailed information on how we collect, use, and protect your personal data.
By using our website, you acknowledge that you have read, understood, and agreed to our Privacy Policy.
If you have any questions or concerns about our Privacy Policy, please contact us at admin@chellu.tech.
Last Updated: 28/06/2023
Chellu Solutions (“we,” “us,” or “our”) is committed to protecting your privacy. This Privacy Policy explains how we collect, use, and safeguard your personal information when you visit our website, www.chellu.tech, or use our services. By accessing or using our website, you consent to the collection, use, and disclosure of your personal information as described in this Privacy Policy. If you do not agree with this policy, please refrain from using our website.
Information We Collect
1.1 Personal Information: We may collect personal information from you when you voluntarily provide it to us. This includes information such as your name, email address, phone number, IP address, and any other relevant details you provide when interacting with our website or services.
1.2 Cookies and Tracking Technologies: We use cookies and similar tracking technologies to enhance your browsing experience, analyze website traffic, and for marketing purposes. These technologies may collect information about your device, browsing actions, and patterns. You have the option to disable cookies through your browser settings, although this may limit certain features and functionality of our website.
How We Use Your Information
2.1 Providing Services: We use the personal information we collect to deliver the services you request, such as processing orders, providing customer support, and delivering personalized content.
2.2 Communication: We may use your personal information to communicate with you, including responding to your inquiries, providing updates about our services, and sending marketing communications with your consent.
2.3 Improving Our Services: We may use your information to analyze trends, track website usage, and gather demographic information to improve our services, website functionality, and user experience.
2.4 Legal Compliance: We may use and disclose your personal information as required by law, regulation, or legal process, or to protect our rights, property, or safety, or the rights, property, or safety of others.
Data Sharing
3.1 Third-Party Service Providers: We may share your personal information with trusted third-party service providers who assist us in operating our website and delivering our services. These providers have access to your information only to perform specific tasks on our behalf and are obligated to keep it confidential.
3.2 Compliance with Law: We may disclose your personal information if required to do so by law or in response to a valid legal request, such as a court order, government inquiry, or regulatory authorities.
3.3 Business Transfers: In the event of a merger, acquisition, or sale of all or a portion of our assets, your personal information may be transferred to the acquiring entity or parties involved as part of the transaction. We will notify you via email and/or prominent notice on our website of any change in ownership or use of your personal information.
Data Security
4.1 Data Protection Measures: We take reasonable technical and organizational measures to protect your personal information from unauthorized access, loss, or destruction. We use industry-standard security protocols, including encryption, firewalls, and secure socket layer (SSL) technology to safeguard your information.
4.2 Data Retention: We retain your personal information for as long as necessary to fulfill the purposes outlined in this Privacy Policy, unless a longer retention period is required or permitted by law.
Your Rights and Choices
5.1 Access and Correction: You have the right to access, update, or correct your personal information. You can do so by logging into your account or contacting us directly.
5.2 Opt-Out: You have the option to unsubscribe from our marketing communications at any time by following the instructions provided in the communication or contacting us directly.
5.3 Do Not Track: Our website does not respond to “Do Not Track” signals or similar mechanisms.
Third-Party Links
Our website may contain links to third-party websites or services. This Privacy Policy does not apply to those websites or services. We encourage you to review the privacy policies of those third parties before providing any personal information.
Children’s Privacy
Our website and services are not intended for children under the age of 13. We do not knowingly collect personal information from children. If you believe that we may have inadvertently collected personal information from a child, please contact us, and we will take steps to delete the information.
Changes to this Privacy Policy
We reserve the right to modify or update this Privacy Policy at any time. Any changes will be effective upon posting the revised version on our website. We encourage you to review this Privacy Policy periodically for any updates.
Contact Us
If you have any questions, concerns, or requests regarding this Privacy Policy or our privacy practices, please contact us at support@chellu.tech